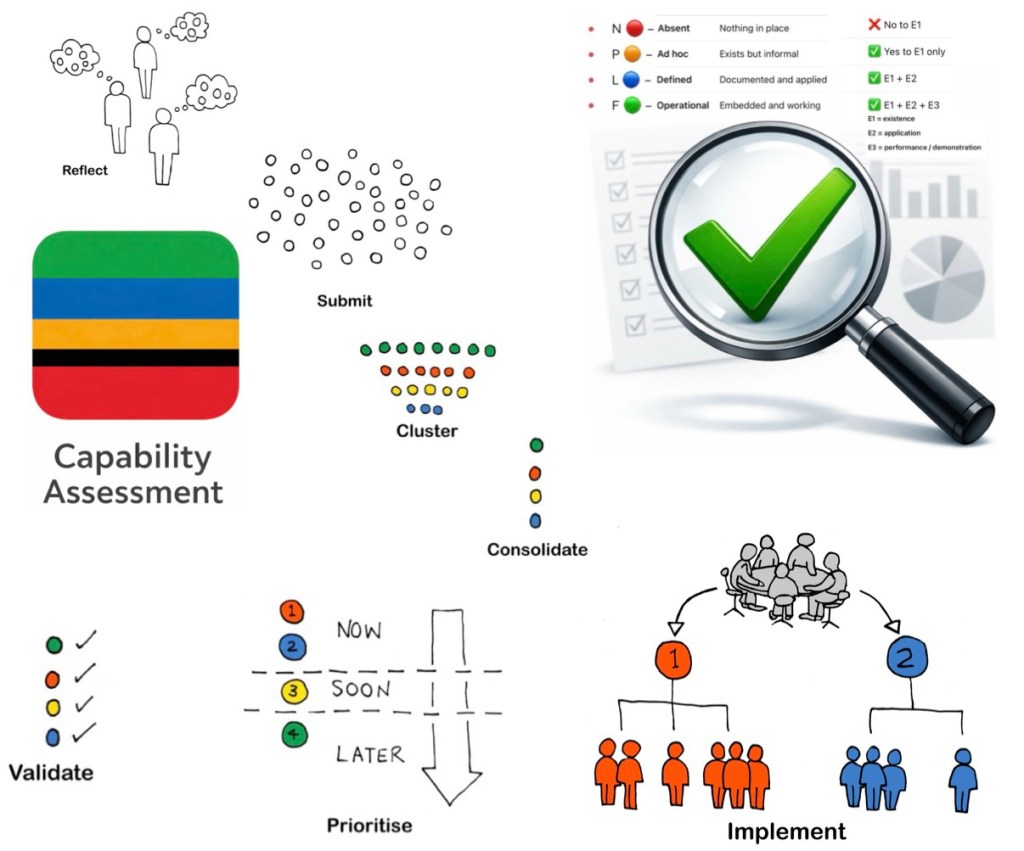
You can treat “necessary and sufficient” at each level as
(a) existence of defined artefacts (E1),
(b) evidence of use and quality (E2), and
(c) evidence that use is routine, linked to other systems, and self‑reinforcing (E3) across all seven domains.[1]
Below are concise criteria you can use as an assessment rubric.
1. BCM Program & Governance
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Approved BCM policy stating objectives, scope, and principles.
- Documented roles, responsibilities, and authorities for BCM (incl. executive sponsor and owner).
- Defined governance structure (e.g., steering committee, risk/BCM forum) with ToR and meeting cadence.
- BCM included in organisational policy hierarchy and referenced in key management system documents.
E2 – Effective
Necessary and sufficient evidence:[1]
- Governance body meeting records showing BCM on the agenda, decisions, and follow‑up actions (priorities, risk acceptance, funding).
- Documented approval of BCM plans, strategies, and key assumptions by governance.
- Evidence of resource allocation decisions for BCM (budget lines, FTE, tools).
- Escalation and issue‑resolution records demonstrating governance intervention on BCM issues.
E3 – Embedded
Necessary and sufficient evidence:[1]
- BCM explicitly integrated into ERM, strategy, and investment processes (e.g., BCM inputs in risk registers and business cases).
- BCM status incorporated into management review, board reporting, and audit/assurance programs.
- BCM accountabilities in executive scorecards or KPIs, and reflected in performance discussions.
- Demonstrated use of BCM insights in strategic decisions (e.g., site selection, outsourcing, IT transformation).
2. BIA & Risk Assessment
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Documented BIA and continuity risk assessment methodology, including impact dimensions, scoring, RTO/RPO definitions, and approval.
- Standard templates and tools for BIAs and risk assessments.
- Defined scope and criteria for critical activities, applications, sites, and third parties.
- Assigned responsibilities and schedule for conducting and reviewing BIAs/assessments.
E2 – Effective
Necessary and sufficient evidence:[1]
- Completed BIAs for in‑scope business units showing clear impact rationales, quantified impacts, and traceable RTO/RPO decisions.
- Risk assessments with documented causes, scenarios, likelihood, and controls leading to coherent risk ratings.
- Evidence that BIA and risk outputs are used in strategy choice (e.g., mapping RTOs to DR tiers, staffing, alternate sites).
- Sign‑off by accountable business owners and challenge/validation by BCM or risk specialists.
E3 – Embedded
Necessary and sufficient evidence:[1]
- BIA and risk data maintained in a living register or system with defined review triggers (e.g., annual plus change‑driven updates).
- Evidence that updated BIA/risk outputs directly drive investment, prioritisation, and project decisions.
- Linkage between BIA/risk results and other disciplines (IT DR planning, vendor risk, crisis scenarios, insurance).
- Regular reporting of BIA and risk metrics/trends to governance and inclusion in audit and assurance scopes.
3. BCM Strategies & Solutions
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Documented organisational approach for selecting continuity/recovery strategies (e.g., tiers, patterns, cost–benefit criteria).
- Defined decision criteria linking strategies to RTO/RPO, risk appetite, and dependencies (people, facilities, IT, suppliers).
- Standard templates for documenting strategy options, assumptions, and decisions.
- Roles and approvals for endorsing BCM strategies.
E2 – Effective
Necessary and sufficient evidence:[1]
- Strategy documents demonstrating realistic solutions mapped to agreed RTOs/RPOs and constraints.
- Technical and operational validation that strategies are feasible (e.g., DR design, capacity assessments, alternate site readiness).
- Evidence of trade‑off analysis and cost–benefit justification for chosen strategies.
- Sign‑off from affected stakeholders (IT, facilities, HR, suppliers, operations) confirming capability and responsibilities.
E3 – Embedded
Necessary and sufficient evidence:[1]
- Clear alignment of BCM strategies with risk appetite, budgets, IT DR architecture roadmaps, and supplier contracts/SLAs.
- Integration of BCM strategies with broader resilience initiatives (e.g., cyber, supply chain, safety, crisis management).
- Periodic review of strategies tied to architecture, sourcing, and capital planning cycles.
- Evidence that major change programs routinely consider and update BCM strategies as part of their process.
4. BCM Plans & Procedures
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Documented organisational framework for plan types (crisis, business recovery, IT DR, site emergency, etc.) and their relationships.
- Standard templates, style guides, and minimum content requirements for BCM plans.
- Defined ownership, maintenance responsibilities, and review cycles for each plan.
- Formal approval process for plans.
E2 – Effective
Necessary and sufficient evidence:[1]
- Plans that are concise, role‑based, and action‑oriented with clear triggers, decision points, and checklists.
- Inclusion of dependencies, workarounds, communication matrices, and contact lists verified as current.
- Evidence from exercises or incidents that plans could be followed under time pressure and enabled timely recovery.
- Feedback from users indicating plan usability and clarity, and resulting improvements.
E3 – Embedded
Necessary and sufficient evidence:[1]
- Plans stored in accessible locations (including offline/alternate access) and referenced in operational procedures and contracts.
- Demonstrated use of plans during real incidents or exercises (logs, debriefs, post‑incident reports).
- Integration with other documentation sets (SOPs, IT runbooks, HR procedures, vendor playbooks).
- Routine plan updates triggered by organisational changes, system updates, or lessons learned, with version control.
5. Exercising, Testing & Maintenance
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Documented exercising/testing strategy and program with scope, objectives, frequency, and methods (table‑top, simulation, technical tests).
- Defined roles, responsibilities, and approval requirements for exercises and tests.
- Standard templates for scenarios, plans, evaluation, and reporting.
- A forward schedule or calendar of exercises and tests.
E2 – Effective
Necessary and sufficient evidence:[1]
- Executed exercises that test key assumptions, decision‑making, escalation, and recovery timelines against RTOs/RPOs.
- Test and exercise reports capturing objectives, outcomes, issues, and quantitative/qualitative performance.
- Evidence that coordination across functions, sites, and suppliers has been exercised and evaluated.
- Documented comparison of actual recovery performance versus targets, with root‑cause analysis where not met.
E3 – Embedded
Necessary and sufficient evidence:[1]
- Lessons identified captured in a central log with owners, due dates, and status tracking to closure.
- Evidence that lessons directly trigger updates to BIAs, strategies, plans, training, and technical configurations.
- Exercises integrated into business calendars (e.g., aligned to peak periods, change freezes, regulatory cycles).
- Continuous improvement themes visible over time (e.g., recurring issues reducing, maturity increasing in reports).
6. Culture, Training & Awareness
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Defined BCM roles (e.g., coordinators, plan owners, incident managers) with competency profiles.
- Organisational BCM training and awareness framework, including curricula for different role types.
- Training materials and awareness artifacts (e‑learning, slide decks, intranet content, posters, FAQs).
- Defined schedule and responsibility for delivering and maintaining training and awareness.
E2 – Effective
Necessary and sufficient evidence:[1]
- Training records showing completion rates by role, with assessments or quizzes indicating competence.
- Evidence that participants can perform critical BCM tasks during exercises or incidents (observed behaviours, role performance).
- Feedback mechanisms (surveys, debriefs) indicating understanding of BCM responsibilities.
- Demonstrated engagement from leaders (sponsoring sessions, speaking at drills, messaging on BCM importance).
E3 – Embedded
Necessary and sufficient evidence:[1]
- BCM awareness integrated into onboarding, role changes, and periodic refresher programs.
- Regular leadership communications referencing BCM and resilience as part of “how we do business”.
- BCM behaviours visible in day‑to‑day operations (e.g., staff raising resilience issues, using workarounds, updating call‑trees).
- BCM competence referenced in role descriptions, performance reviews, or professional development plans.
7. Performance Evaluation & Continuous Improvement
E1 – Established (gateway)
Necessary and sufficient evidence:[1]
- Documented mechanisms for monitoring, measuring, and evaluating BCM (KPIs, KRIs, internal audits, management reviews).
- Defined BCM metrics set (e.g., BIA coverage, test performance, plan currency, training rates).
- Schedule and roles for BCM performance evaluations and reviews.
- Linkage to nonconformance/corrective action processes where they exist.
E2 – Effective
Necessary and sufficient evidence:[1]
- Regular reports that identify meaningful gaps, trends, and systemic weaknesses (not just activity counts).
- Internal audits or reviews with documented findings, ratings, and recommendations related to BCM.
- Evidence that performance information is discussed by governance, with prioritised actions agreed.
- Analysis across incidents, tests, and metrics demonstrating insight into underlying causes, not just symptoms.
E3 – Embedded
Necessary and sufficient evidence:[1]
- Corrective and improvement actions tracked through to closure with deadlines and accountability.
- Evidence that BCM evaluation outcomes influence management decisions, investment, and risk appetite discussions.
- BCM performance integrated into enterprise assurance maps and combined assurance reporting.
- Demonstrated year‑on‑year changes in capability, reflected in metrics, external feedback, or independent maturity assessments.
Reference Source
[1] Business-Continuity-Management-2.pdf